Firewalld
firewalld provides a dynamically managed firewall with support for network “zones” to assign a level of trust to a network and its associated connections and interfaces. It has support for IPv4 and IPv6 firewall settings. It supports Ethernet bridges and has a separation of runtime and permanent configuration options. It also has an interface for services or applications to add firewall rules directly.
Network Zones
Firewalls can be used to separate networks into different zones based on the level of trust the user has decided to place on the devices and traffic within that network. NetworkManager informs firewalld to which zone an interface belongs. An interface’s assigned zone can be changed by NetworkManager or via the firewall-config tool which can open the relevant NetworkManager window for you.
The zone settings in /etc/firewalld/ are a range of preset settings which can be quickly applied to a network interface.
- drop: The lowest level of trust. All incoming connections are dropped without reply and only outgoing connections are possible.
- block: Similar to the above, but instead of simply dropping connections, incoming requests are rejected with an icmp-host-prohibited or icmp6-adm-prohibited message.
- public: Represents public, untrusted networks. You don’t trust other computers but may allow selected incoming connections on a case-by-case basis.
- external: External networks in the event that you are using the firewall as your gateway. It is configured for NAT masquerading so that your internal network remains private but reachable.
- internal: The other side of the external zone, used for the internal portion of a gateway. The computers are fairly trustworthy and some additional services are available.
- dmz: Used for computers located in a DMZ (isolated computers that will not have access to the rest of your network). Only certain incoming connections are allowed.
- work: Used for work machines. Trust most of the computers in the network. A few more services might be allowed.
- home: A home environment. It generally implies that you trust most of the other computers and that a few more services will be accepted.
- trusted: Trust all of the machines in the network. The most open of the available options and should be used sparingly.
To use the firewall, we can create rules and alter the properties of our zones and then assign our network interfaces to whichever zones are most appropriate.
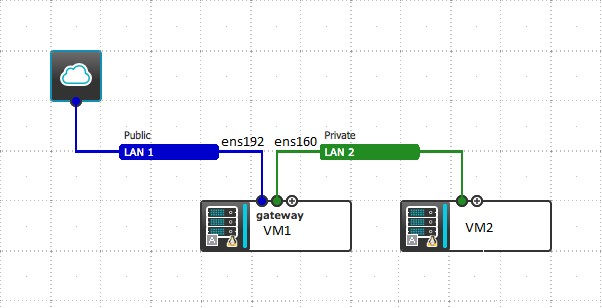
How to enable FirewallD Simple NAT on your CentOS7
You can Enable Outbound simple NAT on FirewallD using centos7 server.
Start your Firewalld
# systemctl start firewalld.service
Enable IP Forwarding
sysctl -w net.ipv4.ip_forward=1Check with your network interface.
ens160: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.10 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::20c:29ff:fecc:ac0c prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:cc:ac:0c txqueuelen 1000 (Ethernet)
RX packets 354931 bytes 23015677 (21.9 MiB)
RX errors 0 dropped 52 overruns 0 frame 0
TX packets 6896 bytes 626333 (611.6 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
ens192: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 104.24.101.150 netmask 255.255.255.224 broadcast 104.24.101.145
inet6 fe80::20c:29ff:fecc:ac16 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:cc:ac:16 txqueuelen 1000 (Ethernet)
RX packets 537458 bytes 41460161 (39.5 MiB)
RX errors 0 dropped 59 overruns 0 frame 0
TX packets 195260 bytes 47842690 (45.6 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
We are using ens160 as private network and ens192 as public network.
Check your firewalld current lists on your VM1
# firewall-cmd --list-all
# firewall-cmd --list-all --zone=external
Add public interface as public zone permanent.
# firewall-cmd --change-interface=ens192 --zone=external --permanent
Restart Firewalld
# firewall-cmd --complete-reload
# firewall-cmd --list-all --zone=external
Configure private as internal zone permanent.
# firewall-cmd --change-interface=ens160 --zone=internal --permanent
Configure internal zone as default
# firewall-cmd --set-default-zone=internal
Restart Firewalld
# firewall-cmd --complete-reload
Add DNS service as permanent
# firewall-cmd --zone=internal --add-service=dns --permanent
# firewall-cmd --complete-reload
You can verify external zone
# firewall-cmd --list-all --zone=external
Done.
Login your Private Network server and configure the ens160 IP address as the gateway.
# ssh [email protected]
ping your external network
ping google.com
Example video